How to Protect WordPress from malware?

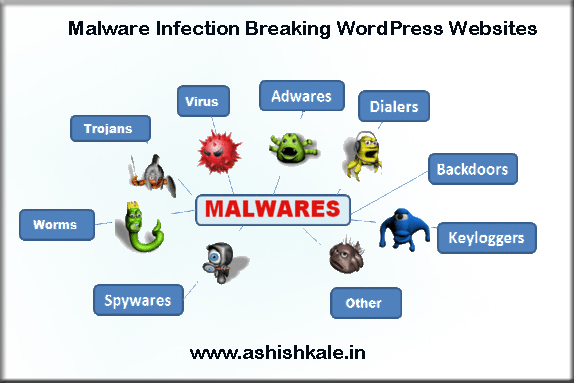
Malware WordPress is installed on so many websites now, the global reach is comparable to a company like Microsoft. You probably already know the word malware from PC’s and computers. Computer viruses have been around a long time, as well as virus scanning software. With the Internet age came spyware (programs that spy on what you do and send […]
» Read more